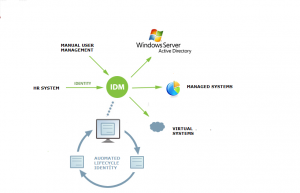
Jak napojit MS AD do CzechIdM v 5 jednoduchých krocích?
V dalším článku vás necháme nahlédnout pod pokličku verze CzechIdM, která ještě není na světě, ale vyjde během několika málo dní. CzechIdM 10.8. bude přebírat štafetu příznaku LTS (long term support). Pokračujeme v ní v práci na zlepšování UX, tentokrát jsme připravili Wizard jak napojit MS AD k CzechIdM. V jednom z předešlých článků jste […]
25. 2. 2021 • Marcel Poul