How to connect Microsoft Active Directory into CzechIdM
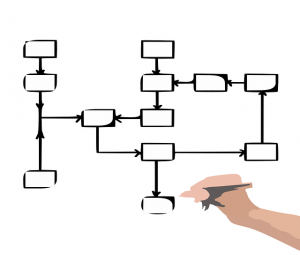
Since MS AD is the major directory service spread across the enterprise environment, connecting it to our identity manager CzechIdM is one of the most frequent task we come across. This text is a short tutorial of how to manage accounts of users in AD via an identity manager CzechIdM. It will guide you through […]
11. 4. 2018 • Marcel Poul